Table of Contents
SITREP Link to SITREP
Several employees reported that they were unable to log into Outlook. Additionally, the Exchange system administrator discovered that they could not access the Exchange Admin Center. Upon initial triage, they found multiple suspicious README files on the Exchange server.
Below is a copy of the ransomware note: 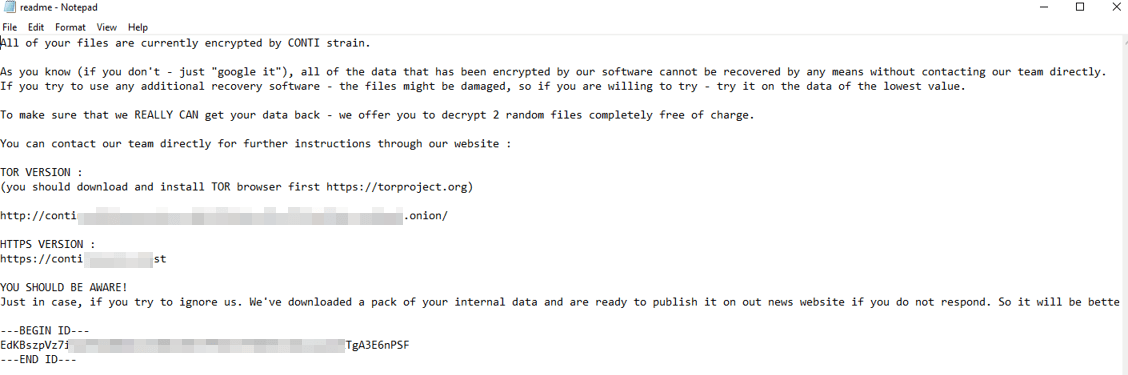
Read the latest information on the Conti ransomware here.
Exchange Server Compromised Link to Exchange Server Compromised
Below are the error messages encountered by the Exchange administrator and employees when attempting to access Exchange or Outlook.
Exchange Control Panel: 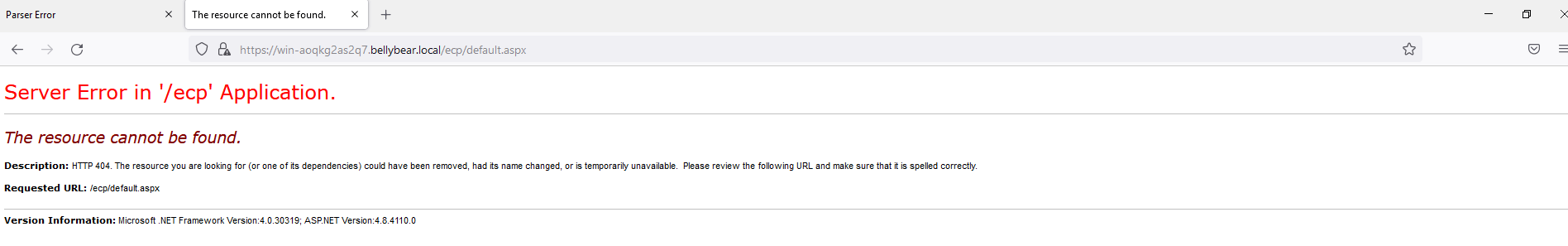
Outlook Web Access: 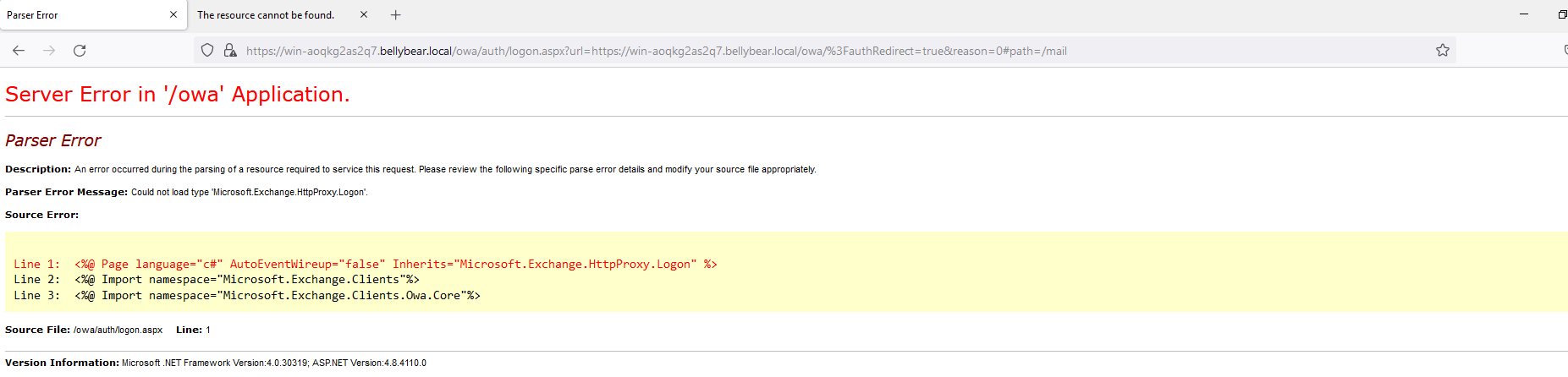
Task: You have been assigned to investigate this incident. Use Splunk to answer the questions below regarding the Conti ransomware attack.
Question 1: Can you identify the location of the ransomware? Link to Question 1: Can you identify the location of the ransomware?
The hint suggests looking for a common Windows binary in an unusual location. To identify this, I launched Splunk and set the timestamp to All time. Among the four available sourcetypes, I selected WinEventLog:Microsoft-Windows-Sysmon/Operational. Searching for executable files within user directories, I found the ransomware under the Administrator’s Documents folder disguised as cmd.exe—an unusual location.
Command used:
12sourcetype="WinEventLog:Microsoft-Windows-Sysmon/Operational"
| search Users AND image: ".exe"
View Answer
Question 2: What is the Sysmon event ID for the related file creation event? Link to Question 2: What is the Sysmon event ID for the related file creation event?
The question asks for the event code associated with file creation. Sysmon logs file creation events under EventCode 11. We can confirm this by filtering events based on EventCode.
Command used:
12sourcetype="WinEventLog:Microsoft-Windows-Sysmon/Operational"
| search Users AND image: ".exe" AND EventCode
View Answer
Question 3: Can you find the MD5 hash of the ransomware? Link to Question 3: Can you find the MD5 hash of the ransomware?
To retrieve the MD5 hash of the ransomware executable (cmd.exe), we can filter for hashes in the logs.
Command used:
12sourcetype="WinEventLog:Microsoft-Windows-Sysmon/Operational"
| search Users AND image: "C:\Users\Administrator\Documents\cmd.exe" AND "Hashes"
View Answer
Question 4: What file was saved to multiple folder locations? Link to Question 4: What file was saved to multiple folder locations?
To determine which file was saved in multiple locations, I filtered logs for EventCode 11 and used the table command to display only the TargetFileName field.
Command used:
12EventCode=11
| table TargetFileName
View Answer
Question 5: What command did the attacker use to add a new user to the compromised system? Link to Question 5: What command did the attacker use to add a new user to the compromised system?
To find this, I searched for Sysmon logs where the command included /add.
Command used:
12sourcetype="WinEventLog:Microsoft-Windows-Sysmon/Operational" AND "/add"
| table _time, CommandLine
View Answer
Question 6: What was the migrated process image, and what was the original process image? Link to Question 6: What was the migrated process image, and what was the original process image?
By filtering for EventCode 8, I identified the process migration details.
Command used:
1sourcetype="WinEventLog:Microsoft-Windows-Sysmon/Operational" AND EventCode=8
View Answer
Question 7: What process image was used to retrieve system hashes? Link to Question 7: What process image was used to retrieve system hashes?
From the logs, the lsass.exe process was used to retrieve system hashes.
View Answer
Question 8: What web shell did the exploit deploy? Link to Question 8: What web shell did the exploit deploy?
The hint suggests checking IIS logs for POST requests.
Command used:
1sourcetype="WinEventLog:Application" AND "request"
View Answer
Question 9: What command executed the web shell? Link to Question 9: What command executed the web shell?
To locate this, I searched for command-line executions related to i3gfPctK1c2x.aspx.
View Answer
Question 10: What three CVEs were leveraged in this exploit? Link to Question 10: What three CVEs were leveraged in this exploit?
View Answer
Conclusion Link to Conclusion
In conclusion, this investigation provided a comprehensive analysis of the Conti ransomware attack on the Exchange server. By leveraging Splunk for log analysis, we identified key attack indicators, including the ransomware’s location, event logs, malicious commands, and exploited vulnerabilities. Understanding these attack patterns enhances our ability to detect, mitigate, and prevent similar threats in the future.
Conti
© EveSunMaple | CC BY-SA 4.0